The Cybersecurity field, in all its dimensions, is exponentially growing, evolving and expanding. New security risks emerge with the continuous increase of Internet interconnections and the development of the Internet of Things. Cyberattacks endanger individuals and companies, as well as vital public services and infrastructures. Confronted with spreading and evolving cyber threats, organizations and individuals are falling behind in defending their systems and networks, and they often fail to implement and effectively use basic cybersecurity and privacy practices and technologies.
The 3rd International conference on HCI for Cybersecurity, Privacy, and Trust (HCI-CPT) intends to help, promote and encourage research in this field by providing a forum for interaction and exchanges among researchers, academics, and practitioners in the fields of HCI and cyber security. The Conference addresses HCI principles, methods and tools in order to address the numerous and complex threats which put at risk computer-mediated human-activities in today’s society, which is progressively becoming more and more intertwined with and dependent on interactive technologies.
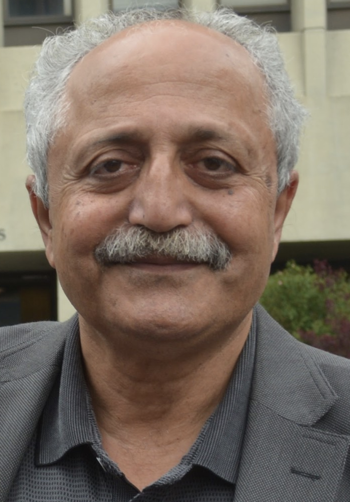
Abbas Moallem
Charles W. Davidson College of Engineering,
San Jose State University, USA